Miss MacDonald's email was HTML only, constructed by a script. As rendered
by w3m, the text of the message was as follows:
|
Hello, I'm trying to get the word out about my website, christiandatingsites.net. Would you consider adding a link to my site from your website danbyrnes.com.au/legal.htm? I'm Cindy McDonald, and I own a site called christiandatingsites.net, for which I'm also a blogger. christiandatingsites.net is the only website exclusively devoted to Christian singles who want reliable information about avoiding the financial and physical dangers inherent in using online dating, serving our readers by authoring articles on topics like how to identify dating site scams and how to deal with one if you fall victim. Please don't hesitate to ask questions; I'm available via email to address any concerns you may have. Thank you for your time and consideration, Cindy McDonald |
Now before replying to Cindy, your blogger's eyes, as always, strayed
towards the email headers ... You may recall dear reader, that your blogger
uses an MUA called mutt, which is an exceptionally humble little canine that
does absolutely nothing with fancy HTML, in fact your blogger had to pipe the
body to w3m in order to render the content ... But mutt does a superb job of
rendering email headers in great detail ... And your humble blogger has
reproduced them below, with some email portions strategically 'x'ed out ...
|
From anonymous@trackingmetrics.info Tue Feb 21 08: 6:31 2012 Return-Path: <trackingmetrics.info> X-Spam-Checker-Version: SpamAssassin 3.3.1 (2010-03-16) on pgts04 X-Spam-Level: ** X-Spam-Status: No, score=2.6 required=5.0 tests=BAYES_50, HTML_IMAGE_ONLY_16, HTML_MESSAGE,MIME_HTML_ONLY, URIBL_RED autolearn=no version=3.3.1 X-Original-To: xxxxx@pgts.com.au Delivered-To: xxxxx@pgts.com.au Received: from trackingmetrics.info (medicalmalpracticelawyers.org [72.10.51.124]) by pgts04.pgts.com.au (Postfix) with ESMTPS id 88CF63E0100 for <xxxxx@pgts.com.au>; Tue, 21 Feb 2012 08:06:29 +1100 (EST) Received: (qmail 30066 invoked by uid 48); 20 Feb 2012 12:28:19 -0800 Date: 20 Feb 2012 12:28:19 -0800 Message-ID: <2819.30064.qmail@trackingmetrics.info> To: xxxxx@pgts.com.au Subject: Website question X-PHP-Originating-Script: 10006:test_email.php From: Cindy McDonald <nald@christiandatingsites.net> MIME-Version: 1.0 Content-Type: text/html; charset=ISO-8859-1 |
And so your blogger contemplated whether he should assist Cindy or perhaps just drop her a short little note and explain that he wasn't actually the webmaster for the site she mentioned although he would be happy to pass along her details ... And perhaps, in passing, to offer some friendly advice that she should be careful about the company she keeps. In particular, the type of agencies that she employed for her online promotions. Because under most circumstances when your blogger saw email headers as funky as hers, he would most likely set the dogs on her. Especially in light of many recent studies which have shown that although advance fee fraud was the most popular Internet scam, dating scams were the most costly (for the victims), and on the increase ... And furthermore, had it not been for the good Christian content of her (email) body, Spam Assassin might have come out of its kennel and sunk its Bayesian teeth into her shapely rear-end ... Although had this occurred, your blogger would not have had the pleasure of reading Cindy's email ... As Cindy was obviously engaged in good Christian work, the funky headers had probably been an over-sight on her behalf ...
Your blogger's reverie about shapely, nubile Christians was interrupted at this stage ... By another, practically identical, email from the same source, which arrived almost half an hour later, at 08:31:59 Australian Eastern Standard Time.
Ok, your humble blogger thought, No more Mr. Nice Guy ...
And unleashed the dogs ... The ever nimble Spam Assassin made note of the
content and the firewall watch dog was alerted about the originating host.
Subsequent investigation tonight reveals that the next email that arrived from
this particular host (after almost half an hour again? They were keen to get
the message across!) ... Did not fare quite so well:
|
Feb 21 08:52:30 pgts04 postfix/smtpd[28335]: NOQUEUE: reject: RCPT from medicalmalpracticelawyers.org[72.10.51.124]: 554 5.7.1 <medicalmalpracticelawyers.org[72.10.51.124]>: Client host rejected: Access denied; from=<anonymous@trackingmetrics.info> to=<xxxxx@pgts.com.au> proto=ESMTP helo=<trackingmetrics.info> |
That seems to be the last your humble blogger has seen from MEDICALMALPRACTICELAWYERS.ORG (owned by MEDIATEMPLE.NET).
TRACKINGMETRICS.INFO is registered by GoDaddy.com LLC. The registered address is in Scottsdale Arizona. Their primary DNS is owned by MEDIATEMPLE.NET.
The domain MEDICALMALPRACTICELAWYERS.ORG is registered by Tucows Inc. with an address in Woodland Hills CA. Their primary DNS is also owned by MEDIATEMPLE.NET.
The address 72.10.51.124 is owned by MEDIATEMPLE.NET, which is registered by GoDaddy.com with an address in Culver City, CA.
American law enforcement agencies who might be interested in their activities may want to examine how strictly they comply with US laws regarding SPAM.
Hopeful business owners that have paid to put links on these and associated networks may want to consider that being associated with spam may tarnish their reputation.
Update 2012-02-23 Spam Surge For February
Research on SPAM, conducted several years ago by a team at Berkeley indicated that SPAM would eventually peak due to economic constraints, namely the ROI (Return On Investment). The greatest overhead spammers face is setup and programming costs. And despite how much they try to talk up their ROI, spammers are severely constrained by the low conversion rate of their business model. Spam organisations that have extensive networks and human resources have been trying to overcome this by legitimising their business ... By turning their hand to normal commerce rather than criminal activities ... An activity that they find difficult because their lists are mostly obtained by suspicious means ... Or by selling their lists to other spammers or wannabes (contact billions of potential customers with our network etc!).
Statistics gathered by this site indicate that SPAM may have peaked in 2011. Although there does seem to be an annual cycle to the data gathered so far.
Preliminary results for this year indicate a surge in spam starting this month.
select to_char(date_trunc('month',incident_time),'yyyy-mm'),count(*) from badguy where bad_type = 'SMTP' and incident_time > '2007-12-31 23:59:59' -- and to_zone like '%pgts.com.au' group by date_trunc('month',incident_time); |
The bar-graph below has been created from the above query. This represents SPAM for the last 50 months.
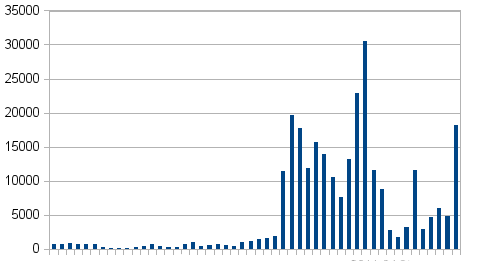
Consolidated SPAM (all domains hosted by PGTS DNS) from 200-08-01 to
present.
Caveat: MTA stats (SPAM rejected by the MTA with block lists) have only been gathered for the past two years, this why there was a sudden jump in the graph above (about 24 monts ago). A more comprehensive graph will be available at the end of this year.
Note: Interested readers who wish to read the most recent research papers from the Berkeley group who analysed SPAM ROI should Google for: Spamalytics Marketing Conversion.
 G. Patterson. T/A PGTS ABN: 99885392845
G. Patterson. T/A PGTS ABN: 99885392845